-
Program officials also say they’ll “reimagine” their upgrade plan, with new delays for some capabilities.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
A previously undocumented “flexible” backdoor called Kapeka has been “sporadically” observed in cyber attacks targeting Eastern Europe, including Estonia and Ukraine, since at least mid-2022. The findings come from Finnish cybersecurity firm WithSecure, which attributed the malware to the Russia-linked advanced persistent threat (APT) group tracked as Sandworm (aka APT44 or
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Security researchers at Cado Security Labs have uncovered a new variant of the Cerber ransomware targeting Linux systems.
This strain of the notorious malware has been observed exploiting a recent vulnerability in the Atlassian Confluence application to gain a foothold on targeted servers.
CVE-2023-22518: The Vulnerability Exploited
The primary attack vector for this Cerber variant is the exploitation of CVE-2023-22518, a vulnerability in the Atlassian Confluence application that allows an attacker to reset the application and create a new administrative account, as reported by Cado Security Labs.
This flaw, disclosed and patched earlier this year, has become a prime target for threat actors seeking to compromise Confluence servers.
Technical Details
The Cerber Linux ransomware is a highly obfuscated C++ payload, compiled as a 64-bit Executable and Linkable Format (ELF) binary and packed with the UPX packer.
This technique is employed to prevent traditional malware scanning and analysis.
Once the attacker gains access to the Confluence server through the CVE-2023-22518 exploit, they use the newly created administrative account to upload and install a malicious web shell plugin, Effluence.
Free Live Webinar for DIFR/SOC Teams: Securing the Top 3 SME Cyber Attack Vectors - Register Here.This web shell provides a user interface for executing arbitrary commands on the compromised host.
Recreation of installing a web shell on a Confluence instance The primary Cerber payload is then downloaded and executed through the web shell.
This payload is a stager responsible for setting up the environment and fetching additional components, including a log checker and the final encryptor payload.
The log checker payload, known as “agttydck,” is a simple C++ program that attempts to write a “success” message to a file.
This is likely a check for the appropriate permissions and sandbox detection.
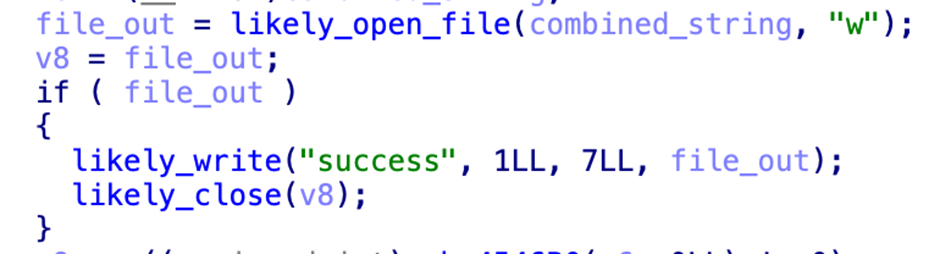
A cleaned-up routine that writes out the success phrase The final encryptor payload, “agttydcb,” is the core of the ransomware.
It systematically encrypts files across the file system, overwriting the original content with the encrypted data and appending the “.L0CK3D” extension.
A ransom note is also left in each directory, demanding payment for the decryption of the files.
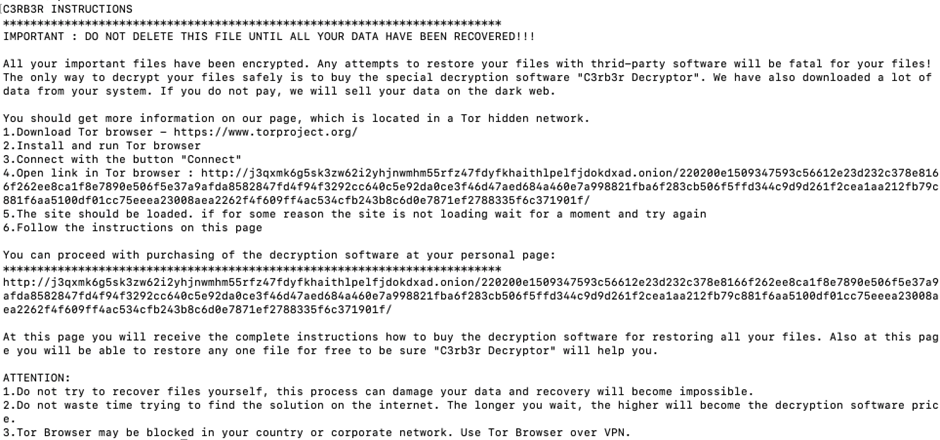
The ransom note left by Cerber The Cerber Linux ransomware exploited the Atlassian Confluence vulnerability, highlighting the importance of timely patching and vigilance in securing critical enterprise applications.
As threat actors continue to target vulnerabilities in popular software, organizations must remain proactive in their security measures to protect against such sophisticated attacks.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAPThe post Cerber Linux Ransomware Exploits Atlassian Servers to Take Full Control appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Detecting source code vulnerabilities aims to protect software systems from attacks by identifying inherent vulnerabilities.
Prior studies often oversimplify the problem into binary classification tasks, which poses challenges for deep learning models to effectively learn diverse vulnerability characteristics.
To address this, the following cybersecurity analysts introduced FGVulDet, a fine-grained vulnerability detector that employs multiple classifiers to discern various vulnerability types:-
- Shangqing Liu from Nanyang Technological University
- Wei Ma from Nanyang Technological University
- Jian Wang from Nanyang Technological University
- Xiaofei Xie from Singapore Management University
- Ruitao Feng from Singapore Management University
- Yang Liu from Nanyang Technological University
FGVulDet Vulnerability Detector
Each classifier learns type-specific semantics, and researchers propose a novel data augmentation technique to enhance diversity in the training dataset.
Inspired by graph neural networks, FGVulDet utilizes an edge-aware GGNN to capture program semantics from a large-scale GitHub dataset encompassing five vulnerability types.

Five Vulnerability Types Previous works have simplified the identification of source code vulnerability into a binary classification problem where all defect-prone functions are labeled as 1.
This approach lacks accuracy because it does not consider types of particular vulnerabilities.
However, in contrast to this, the researchers’ approach focuses on fine-grained vulnerability identification and aims to learn prediction functions for distinct vulnerability types within a dataset.
Each function is categorized based on its vulnerability type to predict its vulnerability status.
Their framework has three core parts:-
- Data Collection
- Vulnerability-preserving Data Augmentation
- Edge-aware GGNN
On the other hand, researchers train multiple binary classifiers for different vulnerability types and aggregate their predictions through voting during the prediction phase.
This task is difficult as obtaining high-quality datasets covering a broad range of vulnerabilities requires specialist knowledge.
.webp)
The framework of FGVulDet (Source – Arxiv) GGNN is a very famous source code modeling approach that is limited to node representations without considering the edge information.
In this case, it’s aimed at proposing an edge-sensitive GGNN that can effectively use edge semantics in vulnerability detection.
Each type of vulnerability has its own binary classifier, which is trained by using datasets of both vulnerable and non-vulnerable functions.
The final prediction is made through majority voting across all the classifiers.
Since the researchers’ dataset includes common vulnerabilities so, it can be extended for detecting others as well.
On the other hand, FGVulDet employs multiple classifiers and a novel data augmentation technique for effective fine-grained vulnerability detection.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post FGVulDet – New Vulnerability Detector to Analyze Source Code appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
DMARC is targeted by hackers as this serves to act as a preventative measure against email spoofing and phishing attempts.
They compromise DMARC (Domain-based Message Authentication Reporting and Conformance) so that they can evade email authentication protocols, consequently enabling them to mimic authentic senders and mislead recipients.
This way they can put up more conceivable and advantageous phishing campaigns that lead to either making money or stealing data.
Cybersecurity researchers at ProofPoint recently discovered that North Korean hackers are actively abusing the DMARC to legitimize their illicit emails.
DMARC Abuse
Proofpoint tracks the North Korean state-aligned group TA427 (aka Emerald Sleet, APT43, THALLIUM, Kimsuky), which conducts phishing campaigns targeting experts on U.S. and South Korean foreign policy for the Reconnaissance General Bureau.
Since 2023, TA427 has directly solicited opinions from foreign policy experts on nuclear disarmament, U.S.-ROK policies, and sanctions via innocent conversation-starting emails.
Free Live Webinar.for DIFR/SOC Teams: Securing the Top 3 SME Cyber Attack Vectors - Register HereResearchers observed a steady and sometimes increasing stream of this activity.
While TA427 consistently relies on social engineering and rotating email infrastructure, in December 2023, it began abusing lax DMARC policies for persona spoofing and incorporated web beacons for target profiling in February 2024.
.webp)
Volume of TA427 phishing campaigns (Source – ProofPoint) TA427 is a skilled social engineering threat actor likely supporting North Korean strategic intelligence collection on U.S. and South Korean foreign policy initiatives.
By engaging targets over extended periods through rotating aliases and innocent conversations, TA427 builds rapport to solicit opinions and analysis, especially around foreign policy negotiation tactics.
Leveraging customized, timely lure content and spoofing familiar DPRK researchers, TA427 requests targets share thoughts via email, papers, or articles rather than directly delivering malware or credential harvesting.
This direct input approach may fulfill TA427’s intelligence requirements while the correspondence insights improve future targeting and connection building for additional engagement.
The goal appears to be augmenting North Korean intelligence to inform negotiation strategies.
.webp)
Timeline of real-world events based on international press reporting (Source – ProofPoint) Their lures include invitations to events on North Korean affairs, inviting perspectives on deterrence policies, nuclear programs, and possible conflicts.
It involves moving conversations between email addresses, such as those of individuals being targeted and their workplaces.
TA427 masks itself in a number of ways as think tanks, non-governmental organizations (NGOs), media outlets, educational institutions, and governmental bodies utilize DMARC abuse, typosquatting, and free email spoofing for legitimization
.webp)
Timeline of real-world events based on international press reporting (Source – ProofPoint) A different tactic from early February 2024 performs reconnaissance over the victim’s active email as well as the recipient environment through web beacons.
One of the most frequently seen actors tracked by Proofpoint is TA427 which constantly adapts its modus operandi, infrastructure elements or even avatars to tactically target experts to steal information or gain initial access for intelligence purposes rather than profit maximization.
IoCs
.webp)
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post North Korean Hackers Abuse DMARC To Legitimize Their Emails appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
A new variant of the Xorist ransomware, dubbed L00KUPRU, has been discovered in the wild, posing a threat to unsuspecting users.
The L00KUPRU ransomware is known to encrypt user files, appending the .L00KUPRU extension to the affected files.
The attackers behind this malware have employed a sophisticated approach, dropping a ransom note as a text file titled “HOW TO DECRYPT FILES.txt.”
This note demands payment in Bitcoin cryptocurrency and displays a pop-up window on the victim’s desktop, providing the attackers’ contact details and the BTC wallet address for the ransom payment.
Free Live Webinar for DIFR/SOC Teams: Securing the Top 3 SME Cyber Attack Vectors - Register Here.Broadcom has published an article detailing its findings on the L00KUPRU ransomware.
The post includes technical details on the malware’s behavior, such as using encryption algorithms and command-and-control servers.
Variant Details
A leading cybersecurity firm has identified several variants of the L00KUPRU ransomware, including:
- Adaptive-based: ACM.Ps-RgPst!g1
- File-based: Ransom.CryptoTorLocker, WS.Malware.1
- Machine Learning-based: Heur.AdvML.B
These variants have been designed to evade detection and infiltrate systems, posing a significant threat to individuals and organizations.
The discovery of the L00KUPRU ransomware is a stark reminder of the ever-evolving landscape of cybersecurity threats.
Experts urge users to remain vigilant, keep their systems and software up-to-date, and implement robust backup strategies to mitigate the impact of such attacks.
Collaboration between security researchers, law enforcement, and the public is crucial in combating the rise of sophisticated ransomware variants like L00KUPRU.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAPThe post L00KUPRU Ransomware Attackers discovered in the wild appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
The introduction of Open AI’s ChatGPT was a defining moment for the software industry, touching off a GenAI race with its November 2022 release. SaaS vendors are now rushing to upgrade tools with enhanced productivity capabilities that are driven by generative AI. Among a wide range of uses, GenAI tools make it easier for developers to build software, assist sales teams in mundane email writing,
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Threat actors are exploiting unpatched Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware. The attacks leverage CVE-2023-22518 (CVSS score: 9.1), a critical security vulnerability impacting the Atlassian Confluence Data Center and Server that allows an unauthenticated attacker to reset Confluence and create an administrator account. Armed with this access, a
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Oracle has released its April 2024 Critical Patch Update (CPU), addressing 372 security vulnerabilities across multiple Oracle products. This comprehensive update fixes critical flaws that could allow remote code execution, data manipulation, and unauthorized access to systems.
Affected Products and Patches
Oracle strongly recommends that users apply the necessary patches as soon as possible to mitigate the risk of potential attacks. The affected products include:
- Oracle Database
- Oracle Fusion Middleware
- Oracle PeopleSoft
- Oracle Siebel CRM
- Oracle Java SE
- Oracle MySQL
- Oracle Retail Applications
- Oracle Financial Services Applications
Users can access the patch updates and detailed information about the vulnerabilities through the Oracle Support port
Free Live Webinar.for DIFR/SOC Teams: Securing the Top 3 SME Cyber Attack Vectors - Register HereKey Highlights
- The April 2024 CPU resolves 372 security vulnerabilities in Oracle products.
- 34 vulnerabilities are classified as “Critical,” with a CVSS score of 9.8 or higher.
- The affected products include Oracle Database, Fusion Middleware, PeopleSoft, Siebel CRM, and Java SE.
Critical Vulnerabilities with 9.8 CVSS Score
The update addresses several critical vulnerabilities with a CVSS score of 9.8, indicating the highest level of severity. These include:
CVE-2024-21234 – Oracle WebLogic Server Remote Code Execution Vulnerability
- Description: Allows remote attackers to execute arbitrary code on vulnerable Oracle WebLogic Server installations.
- CVSS Score: 9.8 (Critical)
- Affected Products: Oracle WebLogic Server versions 12.2.1.4 and earlier.
- Recommendation: Apply the available patch or upgrade to a version that includes the fix.
CVE-2024-21235 – Oracle Fusion Middleware Remote Code Execution Vulnerability
- Description: Allows remote attackers to execute arbitrary code on vulnerable Oracle Fusion Middleware installations.
- CVSS Score: 9.8 (Critical)
- Affected Products: Oracle Fusion Middleware versions 12.2.1.4 and earlier.
- Recommendation: Apply the available patch or upgrade to a version that includes the fix.
CVE-2024-21236 – Oracle Database Server Remote Code Execution Vulnerability
- Description: Allows remote attackers to execute arbitrary code on vulnerable Oracle Database Server installations.
- CVSS Score: 9.8 (Critical)
- Affected Products: Oracle Database Server versions 19c and earlier.
- Recommendation: Apply the available patch or upgrade to a version that includes the fix.
Addressing a Diverse Range of Vulnerabilities
The 372 vulnerabilities addressed in this CPU cover a diverse range of security issues, including:
Database Security Enhancements
The update includes fixes for several vulnerabilities in the Oracle Database, including issues related to SQL injection, privilege escalation, and denial-of-service attacks.
Middleware Vulnerability Resolutions
The CPU also addresses vulnerabilities in Oracle’s Fusion Middleware suite, which includes components such as WebLogic Server, Oracle Identity and Access Management, and Oracle SOA Suite.
Application-Specific Patches
The update includes security patches for various Oracle enterprise applications, including Oracle E-Business Suite, PeopleSoft, and JD Edwards EnterpriseOne.
Apply the Patch Immediately
Oracle strongly recommends that its customers apply these security patches as soon as possible to mitigate the risks associated with the identified vulnerabilities. Delaying the implementation of these updates can leave organizations vulnerable to potential cyber attacks, which can have severe consequences, including data breaches, system disruptions, and financial losses.
“We urge our customers to prioritize the deployment of this Critical Patch Update to ensure the continued security and reliability of their Oracle-based systems,” said Ravi Kumar, Oracle’s Chief Security Officer. “By working together to address these vulnerabilities, we can collectively strengthen the overall security posture of the Oracle ecosystem.”
Customers are advised to refer to the Oracle Security Alert Advisory for more information on the specific vulnerabilities addressed and the recommended actions for deployment.
If Are you from SOC and DFIR Teams, Analyse Malware Incidents & get live Access with ANY.RUN -> Start Now for Free.
The post Oracle Releases Biggest Security Update in 2024 – 372 Vulnerabilities Are Fixed – Update Now! appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
CYBERSECURITY / DEFENSE / INTELLIGENCE


