-
Cisco is warning about a global surge in brute-force attacks targeting various devices, including Virtual Private Network (VPN) services, web application authentication interfaces, and SSH services, since at least March 18, 2024. “These attacks all appear to be originating from TOR exit nodes and a range of other anonymizing tunnels and proxies,” Cisco Talos said. Successful attacks could
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
The Tor Project has released a new version of the Tor Browser, their secure and private web browsing tool. Tor Browser 13.0.14 includes several critical security updates and bug fixes.
Key Updates in Tor Browser 13.0.14
The latest release of Tor Browser focuses on improving users’ security and privacy. Some of the key updates include:
Security Fixes: The update addresses several security vulnerabilities discovered in the underlying Firefox browser engine. These fixes help protect Tor Browser users from potential exploits.
Tor Network Improvements: The release includes updates to the Tor network software to enhance the reliability and performance of the privacy-preserving network.
User Interface Refinements: Minor user interface tweaks and bug fixes improve the overall browsing experience for Tor Browser users.
Free Live Webinar.for DIFR/SOC Teams: Securing the Top 3 SME Cyber Attack Vectors - Register HerePlatforms that Get the Update!
All Platforms
- Updated Tor to version 0.4.8.11
- Addressed the following bugs:
tor-browser#41676: Setprivacy.resistFingerprinting.testing.setTZtoUTCas a defense-in-depth measuretor-browser#42335: Do not localize the order of locales for app languagetor-browser#42428: Timezone offset leak viadocument.lastModifiedtor-browser#42472: Timezone may leak from XSLT Date functiontor-browser#42508: Rebase Tor Browser stable onto 115.10.0esr
Windows, macOS, and Linux
- Updated Firefox to version 115.10.0esr
- Addressed the following bugs:
tor-browser#42172:browser.startup.homepageandTOR_DEFAULT_HOMEPAGEare ignored for the new window opened by New Identitytor-browser#42236: Let users decide whether to load their home page on new identitytor-browser#42468: App languages not sorted correctly in stable
Linux
- Addressed the following bug:
tor-browser-build#41110: Avoid Fontconfig warning about “ambiguous path”
Android
- Updated GeckoView to version 115.10.0esr
- Addressed the following bug:
tor-browser#42509: Backport Android security fixes from Firefox 125
Why Tor Browser Matters for Online Privacy
Tor Browser is a critical tool for anyone looking to browse the web anonymously and protect their online privacy. By routing internet traffic through the Tor network, Tor Browser makes it much harder for users’ activities to be tracked or monitored.
“Tor Browser is an essential tool for journalists, activists, and anyone who values their digital privacy,” said Isabelle Garcia, a spokesperson for the Tor Project. “This latest release ensures Tor Browser remains a secure and reliable way for people to access the internet without compromising their personal information.”
Availability and System Requirements
Tor Browser 13.0.14 is a free download for Windows, macOS, and Linux operating systems. The software can be obtained directly from the Tor Project website at www.torproject.org.
Users will need a computer or mobile device running a compatible operating system to use Tor Browser. Minimum system requirements include at least 100MB of free disk space and 512MB of RAM.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post Tor Browser 13.0.14 Released – What’s New! appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
The Palo Alto Networks PAN-OS software has a critical command injection vulnerability that allows an unauthorized attacker to run arbitrary code on the firewall with root access.
The vulnerability is identified as CVE-2024-3400, with a CVSS score of 10.0. Operation MidnightEclipse has been coined to describe its exploit.
Palo Alto Networks confirmed targeted attacks using this vulnerability last Friday in an alert, crediting a threat actor for known exploitation and noting the possibility of further exploitation by threat actors.
Only PAN-OS 10.2, PAN-OS 11.0, and PAN-OS 11.1 firewalls are configured with device telemetry enabled, and either the GlobalProtect gateway or GlobalProtect portal (or both) are affected by this issue.
Prisma Access, Panorama appliances, and cloud firewalls (Cloud NGFW) are unaffected by this flaw.
How Attackers Exploited The Flaw?
Using the vulnerability, the attackers set up a cron job that retrieves commands hosted on an external server once every minute.
The bash shell is then used to carry out these commands. Palo Alto said the URL is believed to be a delivery system for a firewall backdoor running on Python.
The embedded backdoor component that carries out the threat actor’s directives is decoded and operated by another Python script that is written and launched by the Python file.
Document Stop Advanced Phishing Attack With AI AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Stopping 99% of phishing attacks missed by other email security solutions. .
The threat actor was observed to be remotely exploiting the firewall to download more tooling, establish a reverse shell, change course into internal networks, and eventually steal data.
Palo Alto Networks released a hotfix to address command injection vulnerability in its custom operating system.
The attack was probably the result of a state-sponsored threat actor’s campaign, which security experts discovered began in March.
According to the threat intelligence firm that discovered it, Volexity tracks a threat actor named UTA0218 that started taking advantage of the zero-day vulnerability on March 26.
Based on the resources needed to find and exploit the zero-day, the type of victims targeted, and the complexity of a Python-coded backdoor the threat actors placed to gain additional access to victim networks, Volexity attributes the attack to a government.
According to Volexity, zero-day exploitation appears to be targeted and restricted. However, as of this writing, “evidence of potential reconnaissance activity involving more widespread exploitation aimed at identifying vulnerable systems does appear to have occurred at the time of writing.”
Volexity discovered proof that after the intrusions, the attackers switched to internal networks.
The Active Directory database, as well as browser data from Microsoft Edge and Google Chrome, were among the critical Windows files that the threat actors targeted.
Hotfixes Released
The issue is fixed in hotfix releases of PAN-OS 10.2.9-h1, PAN-OS 11.0.4-h1, PAN-OS 11.1.2-h3, and all later PAN-OS versions.
Additionally, the company said that the hotfixes for commonly deployed maintenance releases will be made available.
Palo Alto Networks advises users to watch for unusual behavior on their networks and investigate any sudden activity.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post Operation MidnightEclipse: Hackers Actively Exploiting Palo Alto Networks Zero-Day Flaw appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Hackers exfiltrate data first before encrypting it to increase their bargaining power during ransom negotiations.
Threats of public exposure of private information accelerate up the urgency for victims to pay a ransom immediately.
Secureworks Counter Threat Unit researchers are tracking the INC Ransom group known as GOLD IONIC.
INC Ransom Group Exfiltrate Data
Emerging in August 2023, this threat group employs double extortion tactics – exfiltrating data before encryption, then threatening public exposure to pressure victims into paying ransoms.
Between August 2023 and March 2024, the Tor leak site of GOLD IONIC published the names of 72 victims, adding 7 in April 2024. It has spread globally despite focusing on American victims from the industrial, healthcare, and education sectors.
Document Stop Advanced Phishing Attack With AI AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Stopping 99% of phishing attacks missed by other email security solutions. .
SecureWorks said that GOLD IONIC seems to be a solo group that encrypts files for ransom rather than having affiliates.
There appears to be a consistent pattern in monthly numbers, with possible exceptions posted as batched releases.
.webp)
Number of victims posted to GOLD IONIC’s leak site from August 2023 through March 2024 (Source – Secureworks) Like many financially motivated groups, GOLD IONIC conducts indiscriminate, opportunistic attacks across geographies and sectors.
However, most victims are U.S.-based organizations, with a significant gap to the second-most impacted country, the UK.
.webp)
Geographic locations of victims posted to GOLD IONIC’s leak site (Source – Secureworks) The prevalence of Western victims and lack of those from Commonwealth of Independent States countries suggests the group likely operates out of Russia or a CIS nation.
No sector stands out, though industrial, healthcare, and education organizations are the most common targets, with educational establishments over-represented compared to other ransomware groups from August 2023 to March 2024.
.webp)
Breakdown of sectors for victims posted to the GOLD IONIC leak site (Source – Secureworks) In Secureworks’ incident response engagements, GOLD IONIC consistently deploys INC ransomware. One case potentially involved initial access via the “Citrix Bleed” vulnerability (CVE-2023-4966), an initial vector favored by LockBit affiliates.
Post-intrusion, the attacker dropped a Meterpreter shell, enumerated Active Directory, archived and exfiltrated over 70GB of data using WinRAR and Megasync, then copied the victim-named INC ransomware binary to over 500 systems and executed it remotely via PsExec to encrypt files.
The INC ransom note instructs contacting the threat actor within 72 hours via a “.onion” address to avoid data leaks.
While the leak site resembles LockBit’s, there are no other known connections between the groups.
%20and%20INC%20Ransom%20(bottom)%20leak%20sites%20(Source%20-%20Secureworks).webp)
Comparison of the LockBit (top) and INC Ransom (bottom) leak sites (Source – Secureworks) The INC Ransom leak site lists some victims of other ransomware groups. One case involved files and a ransom note format matching ALPHV ransomware by GOLD BLAZER.
.webp)
Donut Leaks warning about affiliates posting stolen data to other leak sites (Source – Secureworks) Financially motivated affiliates may act in self-interest, even stealing data to post elsewhere with modified ransom contacts.
Some affiliates have deployed up to seven ransomware families. While the dynamic affiliate-operator relationship could explain cross-posting on leak sites.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post INC Ransom Group Exfiltrates Data Before Encrypting & Threatens Public Exposure appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Over the weekend, Iran launched missile and drone attacks on Israel, retaliating for a suspected Israeli strike on its Damascus consulate that killed 13 people last week.
This escalation arises from the ongoing Israel-Iran rivalry and Israel-Palestine conflict.
Cyber activities predated the attacks by nearly a year, starting in late March when hacktivist groups announced digital offensives against both sides following Hamas’ large-scale offensive from Gaza towards Israel in October 2023 amid intensified Israeli-Palestinian tensions.
The tit-for-tat violence between Israel and Iranian proxies like Hamas shows no signs of decreasing.
SOCRadar observed cyber activities preceding and paralleling the physical Israel-Hamas conflict that began last year.
Once again this week, cyber offensives foreshadowed the missile and drone attacks exchanged between Israel and Iran, demonstrating how cyber warfare often preludes and accompanies kinetic military operations.
Iran’s Attack On Israel
The cyber defense chief Gaby Portnoy of Israel indicated that the cyberattacks targeting Israel tripled since the conflict with Hamas began on October 7, driven by increased involvement from Iran, Hezbollah, and allied hackers.
Document Stop Advanced Phishing Attack With AI AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Stopping 99% of phishing attacks missed by other email security solutions. .
While attack volumes were highest in the conflict’s initial months before tapering, certain days and events saw major spikes in activity.
Recent weeks have witnessed an uptick in hacktivism by groups like OpIsrael and FreePalestine, reflecting the ebbs and flows of cyber offensives paralleling kinetic clashes.
.webp)
Self-claiming Hezbollah-affiliated hacker groups on Telegram carry out various cyber attacks (Source – SOCRadar) A threat on Telegram urged hackers to target Israel during Jewish holidays, citing symbolism in Israeli actions.
Various groups seized on holidays and conflict dates as opportunities for coordinated cyber attacks, SOCRadar said.
While many hacktivists merely signal impending events, wittingly or not, some groups like IRGC-linked, Hezbollah-backed, Iranian APTs, and Houthi hackers had more substantive cyber impacts during the Israel-Hamas conflict.
The allegedly state-sponsored Cyber Toufan/Cyber Toufan Al-Aqsa conducted major operations and coordinated other groups to hit similar targets simultaneously.
After a long break, their activity resurged in early April, potentially foreshadowing the latest Israel-Iran cyber/kinetic escalation.
.webp)
Wake up call of Cyber Toufan Al-Aqsa (Source – SOCRadar) During the Israel-Hamas conflict, a group called Cyber Toufan Al-Aqsa, allegedly sponsored by the state carried out major operations in which it mobilized other groups to hit the same targets simultaneously.
In the start of April this year, they came back after going silent for some time.
In late March, however, IRGC-linked Cyber attackers, popular for attacking OT systems and exposed before they were sanctioned again, reappeared, telling people about an upcoming “big” thing.
They consequently took credit for a huge cyber-attack as payback for Iran’s strikes on Israel.
.webp)
Handala’s alleged hack of Israeli radar systems (Source – SOCRadar) Cyber Av3ngers claimed responsibility for cutting electricity across “occupied territories” from south to north in retaliation for Israeli actions in Gaza.
However, besides this, the widening scope to strike overflow targets like Saudi Arabia demonstrates how easily hacktivism can expand cyber confrontations.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post Iran Launched A Major Cyberattack Against Critical Infrastructure In Israel appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Security researchers have uncovered a new strain of Android malware that masquerades as the popular Google Chrome browser to steal sensitive banking information from unsuspecting users.
The malware, dubbed “Mamont Spy Banker,” has been found to target Android devices highly sophisticatedly.
Mimicking Google Chrome
The malware’s primary tactic is impersonating the Google Chrome app, tricking users into believing they are interacting with a legitimate and trusted application.
This deception is achieved through a nearly identical user interface and branding, making it challenging for even intelligent users to distinguish the malicious app from the real Chrome browser.
According to a recent blog post by GData, a new strain of Android malware has been discovered that impersonates Google Chrome to steal banking credentials.
Document Stop Advanced Phishing Attack With AI AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Stopping 99% of phishing attacks missed by other email security solutions. .
Stealing Banking Details
Once installed, the Mamont Spy Banker malware is designed to intercept and steal sensitive banking information, including login credentials, account numbers, and other financial data.
This information is then siphoned off to the malware’s command-and-control servers, putting victims at risk of financial fraud and identity theft.
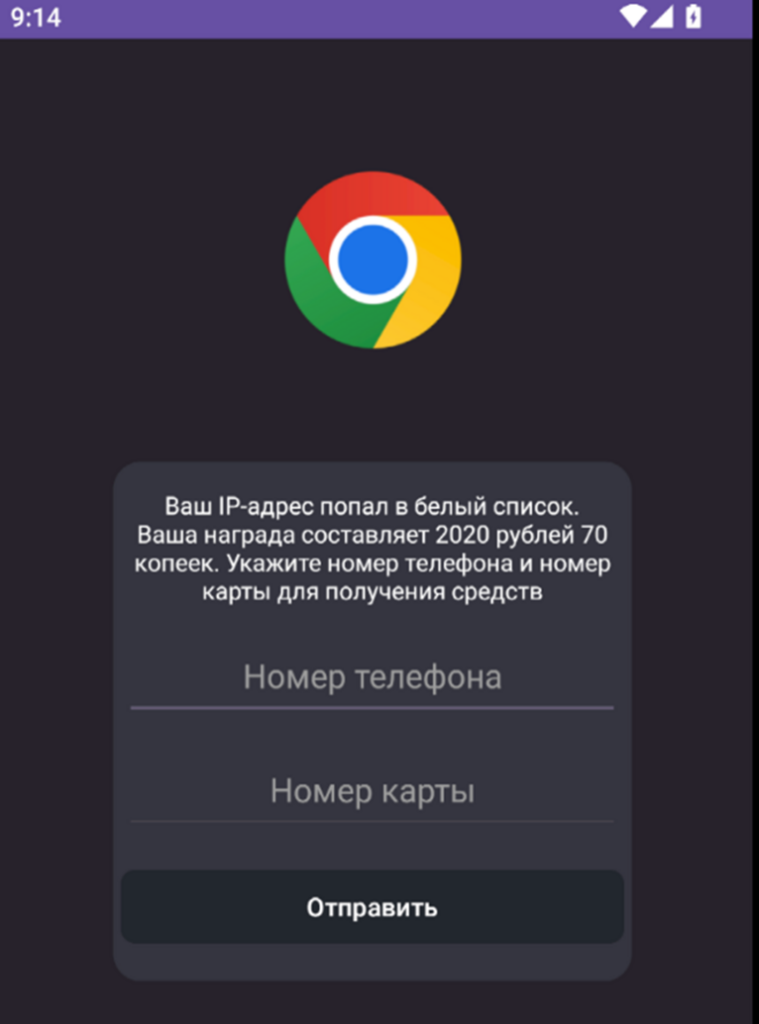
The user will see a text supposedly informing them that they won a cash prize; they are expected to enter their phone and credit card numbers. The researchers at G DATA have noted that the Mamont Spy Banker malware employs sophisticated evasion tactics to avoid detection by traditional security measures.
These include using advanced obfuscation techniques, dynamic code loading, and adapting its behavior based on the device’s environment.
To safeguard against this threat, security experts recommend that Android users exercise caution when downloading and installing apps, even from trusted sources.
Users should also be wary of any apps that closely resemble well-known applications and always verify an app’s legitimacy before granting it access to sensitive information.
Additionally, keeping Android devices up-to-date with the latest security patches and using a reputable antivirus solution can help mitigate the risk of falling victim to this and other emerging Android malware threats.
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAPThe post New Android Malware Mimic Google Chrome to Steal Banking Details appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Hackers target Apple device users because they are perceived to be of higher social classes. This leads to targets who are richer than others and who can possibly provide more money to the hackers in one way or another.
Besides this, Apple’s ecosystem is interconnected, which means it has various points from which hackers can enter, leading to the compromise of accounts and devices.
BlackBerry cybersecurity researchers recently discovered that LightSpy hackers are actively targeting Indian Apple device users to steal sensitive data.
LightSpy Hackers & Their Targets
LightSpy is a modular spying toolkit that can steal victims’ personal information, such as actual GPS coordinates or VOIP calls.
This new threat is dangerous because it allows hackers to follow targets with an exceptional degree of accuracy, expanding the potential impacts of this expansive surveillance on high-profile victims in politically sensitive regions.
LightSpy has an extensive spying capacity and can be used to monitor device data, QQ messenger content, WeChat messages, Telegram chats, and WeChat Pay history.
Document Stop Advanced Phishing Attack With AI AI-Powered Protection for Business Email Security
Trustifi’s Advanced threat protection prevents the widest spectrum of sophisticated attacks before they reach a user’s mailbox. Stopping 99% of phishing attacks missed by other email security solutions. .
This highly effective software program returned during escalated regional hostilities after its 2020 operations had focused on Hong Kong-oriented news websites for distribution.
The threat group, based in servers located in Russia, China, and Singapore, is very interested in monitoring victims involved in clashes of interests across South Asia.
This again highlights how even the slightest flare-ups pose a constant danger to the people involved there.
The motives behind this campaign and the geopolitical implications for Southern Asia that it has raised become sources of worry because of suspected links with China.
Hyper-targeted attacks like these may impact only a tiny fraction of individuals, such as journalists, activists, or politicians, but at the same time can be seen as a worldwide threat.
Tech companies have recently pointed out the danger of state-sponsored election tampering. According to Apple, powerful mercenary spyware is one of the most complex digital threats in existence.
When the vulnerability is detected on news websites specifically reporting Hong Kong issues, the infection usually starts.
.webp)
Loader’s signature (Source – BlackBerry) The attack advances with an initial implant, which collects device data and downloads successive stages.
These include LightSpy, which is the core implant, and special spying plugins.
The Loader starts by loading both the LightSpy kernel in encrypted form and decrypted form, BlackBerry said.
The recent campaign uses “F_Warehouse” framework that has various functionalities including file exfiltration, network reconnaissance, and audio recording.
Besides this, executing shell commands can give full control to an attacker.
While the LightSpy maintains communication with its server as well as with an administrative panel that helps enhance its probable origin.
Recommendations
Here below we have mentioned all the recommendations:-
- Exercise heightened vigilance
- Use of Lockdown mode
- Use highly secure voice and messaging solutions
- Review the latest threat intelligence
- Create an incident response plan
- Update your devices
- Use a passcode
- Enable 2FA
- Beware of unofficial software
- Password hygiene
- Think before you click
- Restart your phone often
Looking to Safeguard Your Company from Advanced Cyber Threats? Deploy TrustNet to Your Radar ASAP.The post LightSpy Hackers Target Indian Apple Device Users To Steal Sensitive Data appeared first on GBHackers on Security | #1 Globally Trusted Cyber Security News Platform.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Carlos Del Toro is asking lawmakers to make it up in a supplemental.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
Service secretary says new initiatives have put the 55,000-recruit goal within reach.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
-
DIU projects promise to ease logistics for Pacific bases and other farflung places.
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
¶¶¶¶¶
CYBERSECURITY / DEFENSE / INTELLIGENCE


